VPC Fundamentals and Core Components
A Virtual Private Cloud (VPC) is a logically isolated network environment within AWS where you launch your resources. Every AWS account has a default VPC, but Solutions Architects must understand how to create and configure custom VPCs for specific use cases.
Core VPC Components
The core components of a VPC include:
- Subnets (public and private) for organizing resources
- Internet Gateways (IGW) for outbound internet connectivity
- Network Address Translation (NAT) gateways for private subnet internet access
- Virtual Private Gateways (VGW) for VPN connections
- VPC endpoints for private connectivity to AWS services
Public vs Private Subnets
Public subnets contain resources accessible from the internet via an Internet Gateway. Private subnets cannot directly access the internet without a NAT gateway. Understanding this distinction is fundamental for designing secure architectures where databases stay isolated from the internet.
CIDR Notation and IP Planning
Understanding CIDR notation is critical because you must calculate IP address ranges for VPCs and subnets. A VPC typically uses a /16 CIDR block (providing 65,536 IP addresses), while subnets use /24 blocks (256 IPs). Multi-AZ deployments require subnets in different Availability Zones for high availability.
Route Tables and Traffic Flow
Route tables determine how traffic flows within the VPC and to external networks. Each subnet must be associated with a route table that specifies where packets with certain destination IPs should be directed. Default routes often point to the Internet Gateway for public subnets or NAT gateways for private subnets.
Security Groups and Network Access Control Lists
Security Groups and Network ACLs (NACLs) form the two-layer firewall system in AWS VPCs, though they operate differently. Understanding both is essential for the exam.
Security Groups: Stateful Firewalls
Security Groups are stateful firewalls at the instance level, meaning they track connections and automatically allow return traffic. When you create an inbound rule allowing TCP traffic on port 80, the Security Group automatically permits the corresponding outbound response traffic without requiring an explicit outbound rule.
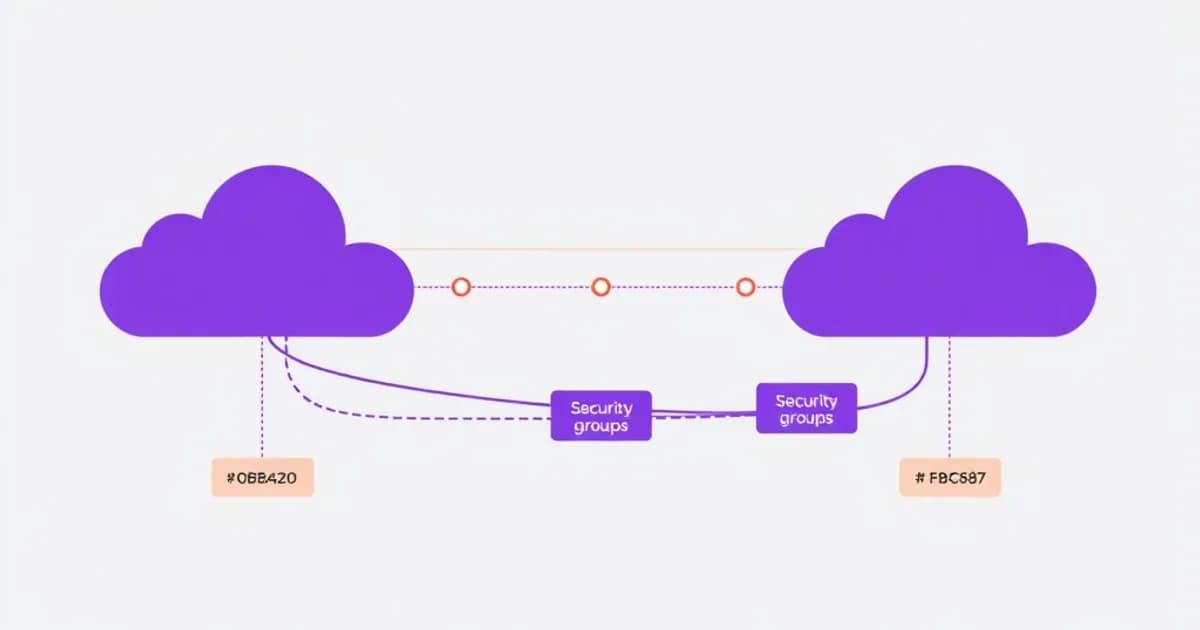
Security Groups use an allow-list model where you must explicitly permit traffic. Anything not explicitly allowed is denied. Security Groups can reference other Security Groups, enabling dynamic rule management when resources are added to the same security group.
Network ACLs: Stateless Firewalls
Network ACLs are stateless firewalls at the subnet level that examine each packet independently without tracking connections. NACLs evaluate rules in numerical order and stop at the first matching rule. This requires you to explicitly allow both inbound and outbound traffic.
Choosing Between Security Groups and NACLs
For the Solutions Architect exam, you should understand when to use each. Use Security Groups for fine-grained instance control and application-layer security. Use NACLs for subnet-level protection and additional defense layers.
A common exam scenario involves restricting SSH access to only specific IP addresses. You would implement this with a Security Group inbound rule allowing TCP 22 from specific CIDR blocks. Another scenario might require allowing ephemeral ports (1024-65535) in an NACL for return traffic.
VPC Connectivity Options and Hybrid Architecture
The Solutions Architect exam extensively covers methods for connecting VPCs to on-premises networks and to other VPCs. Each option has distinct tradeoffs in setup time, cost, and performance.
Site-to-Site VPN
Site-to-Site VPN is the fundamental connection option using encrypted IPSec tunnels over the internet. You establish a Virtual Private Gateway (VGW) on the AWS side and a Customer Gateway on the on-premises side. VPN is quick to set up but performance depends on internet quality.
AWS Direct Connect
AWS Direct Connect provides a dedicated physical connection that offers consistent network performance and lower latency compared to VPN. Setup takes longer and costs significantly more. For exam purposes, remember that Direct Connect is preferred when you need guaranteed bandwidth, low latency, or large data transfer volumes.
VPC Peering and Transit Gateway
VPC Peering connects two VPCs, allowing traffic between them as if they were on the same network. When peering VPCs, you must enable DNS resolution and configure route tables on both sides appropriately.
Transit Gateway is a hub-and-spoke architecture that simplifies connecting multiple VPCs and on-premises networks. It eliminates the need for mesh peering and is essential for large organizations with many VPCs.
VPC Endpoints
VPC endpoints come in two types. Gateway endpoints for S3 and DynamoDB use prefix lists in route tables. Interface endpoints use AWS PrivateLink for accessing other AWS services privately. The exam tests whether you understand the differences in availability, scalability, and cost implications of each connectivity option.
Routing, DNS, and Traffic Management
Route tables are the core routing mechanism in VPCs, determining how packets are directed based on destination IP addresses. Each route consists of a destination CIDR block and a target (Internet Gateway, NAT Gateway, Virtual Private Gateway, peering connection, or transit gateway).
Route Priority and Configuration
Routes are evaluated from most specific to least specific, so a /32 route takes precedence over a /0 route. The local route, which routes traffic within the VPC, is automatically created and cannot be modified. When designing multi-tier architectures, you typically create separate route tables for public and private subnets.
Public route tables include a default route (0.0.0.0/0) pointing to an Internet Gateway. Private route tables route internet traffic through a NAT Gateway in a public subnet. For hybrid architectures, route tables include routes for on-premises CIDR blocks pointing to a Virtual Private Gateway.
DNS and Private Hosted Zones
AWS Route 53, while a managed DNS service, is often referenced in VPC context for DNS failover scenarios. Private hosted zones resolve DNS names only within specific VPCs. This enables you to maintain internal DNS names separate from public DNS.
Traffic Management Beyond Routing
For traffic management beyond basic routing, you can use Network Load Balancers (NLBs) for ultra-high performance and Network Address Translation, or Application Load Balancers for content-based routing. Understanding the difference between static routes (configured manually) and dynamic routes (learned through protocols like BGP with Direct Connect) is essential.
VPC Design Patterns and Best Practices for the Exam
High-availability VPC design requires spreading resources across multiple Availability Zones with redundant components at each layer. A best-practice architecture includes public and private subnets in each AZ with NAT Gateways in each public subnet. This avoids a single point of failure in a single AZ.
Security Best Practices
For security, implement the principle of least privilege by creating specific Security Groups for each tier (web tier, application tier, database tier). Avoid overly permissive rules. Network segmentation through private subnets isolates sensitive resources from the internet. Enable VPC Flow Logs to capture network traffic information for troubleshooting and security analysis.
When designing for compliance requirements like PCI DSS or HIPAA, you must implement proper network isolation. You must also maintain audit trails of network traffic.
Cost Optimization
Cost optimization for VPC involves right-sizing NAT Gateway instances. Remember that NAT Gateways charge per GB of data processed and per hour. Other strategies include consolidating VPCs where possible and using VPC endpoints instead of NAT Gateways for accessing AWS services. The exam often presents scenarios requiring cost-effective network design without sacrificing security or availability.
Common Architectural Mistakes
Common mistakes include creating too many VPCs (increasing operational complexity), insufficient use of private subnets (exposing databases to internet), misconfiguring route tables (causing traffic black holes), and failing to implement redundant NAT Gateways. Practice scenarios that require you to identify and fix these architectural flaws, as the exam frequently includes flawed designs you must critique.