What is the Kubelet and Why It Matters for CKA
The kubelet is a node agent running on every Kubernetes node. It ensures containers execute in pods exactly as specified in the PodSpec manifest.
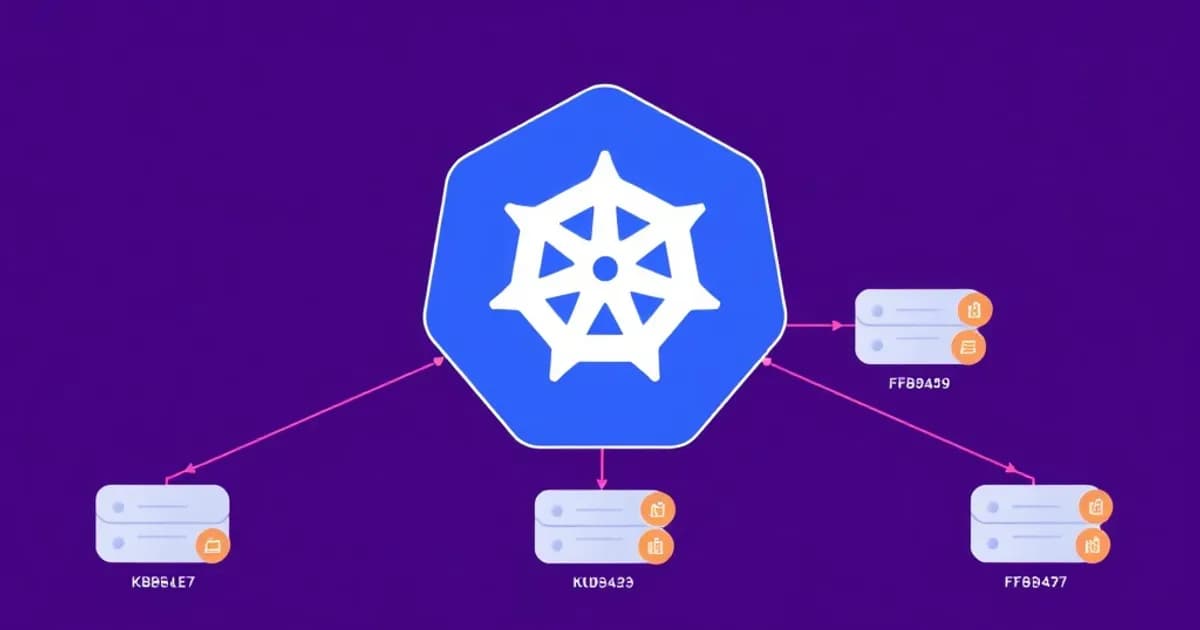
Role in Cluster Architecture
The kubelet sits between the control plane's desired state and actual node execution. It receives pod specifications from the API server, pulls container images, starts containers, and monitors pod health continuously. When something fails, the kubelet automatically handles restarts based on your restart policy.
Why CKA Tests Kubelet Heavily
CKA questions test kubelet frequently because real-world Kubernetes failures trace directly to kubelet misconfiguration. You must diagnose node problems, understand pod scheduling, troubleshoot eviction scenarios, and identify certificate issues.
The kubelet manages multiple critical functions:
- Pulling container images and starting containers
- Implementing liveness probes and readiness probes for health checks
- Handling graceful pod termination with SIGTERM signals
- Managing pod volumes and port mappings
- Enforcing resource limits through the container runtime
Practical Troubleshooting Skills
For CKA success, learn to check kubelet logs using journalctl, review configuration files, and use kubectl describe nodes to identify issues. These hands-on techniques appear repeatedly in exam scenarios.
Kubelet Architecture and Communication Flow
The kubelet operates as a daemon process on each node and maintains constant communication with the Kubernetes API server. This bidirectional communication is essential for a functioning cluster.
API Server Communication Model
The API server watches the node's pod endpoint and pushes pod specifications to the kubelet. The kubelet pulls these specs, creates the necessary pods, and reports node and pod status back to the API server. This watch mechanism ensures the kubelet stays synchronized with cluster state.
The kubelet exposes its own API on port 10250 (default) with endpoints including:
- /pods (list pods on the node)
- /metrics (node metrics)
- /logs (container logs)
TLS Authentication and Security
The kubelet authenticates to the API server using TLS certificates located in /var/lib/kubelet/pki/. Understanding this authentication flow is critical for diagnosing communication failures between nodes and the control plane.
Container Runtime Interface (CRI)
The kubelet implements the Container Runtime Interface abstraction. This allows Kubernetes to work with Docker, containerd, CRI-O, and other runtimes. The kubelet translates PodSpecs into container runtime calls.
Pod Specification Sources
The kubelet handles three sources of pod specifications:
- Static pods (manifest files on the node)
- API server pods (dynamically scheduled)
- HTTP-served pods (less common)
Static pods deserve special attention because they run control plane components on control plane nodes and can't be deleted through the API.
kubectl logs and kubectl exec
When you run kubectl logs or kubectl exec, the API server contacts the kubelet API on port 10250. This is why these commands fail when the kubelet is unreachable.
Kubelet Configuration, Flags, and Troubleshooting
The kubelet configuration controls how nodes behave and directly impacts pod scheduling and resource management. Modern deployments use configuration files at /etc/kubernetes/kubelet/kubelet-config.yaml, specified via the --config flag.
Critical Configuration Parameters
Understanding these parameters is essential for CKA:
- kubeAPIQPS: API server query rate (controls how frequently the kubelet queries the API)
- kubeReserved: Resources reserved for kubelet and system processes
- systemReserved: OS-level resource reservations
- maxPods: Maximum pods per node (default 110)
- podPidsLimit: Process ID limit per pod
- node-status-update-frequency: How often the kubelet reports status (default 10 seconds)
These settings directly impact pod eviction, scheduling decisions, and cluster stability.
Troubleshooting with Logs
The kubelet logs are your first diagnostic tool. On systemd systems, stream logs in real-time:
journalctl -u kubelet -f
Diagnosing Common Issues
Watch for these frequent failure scenarios:
- Kubelets not registering with the API server (check network and certificates)
- Pods stuck in Pending state (verify kubeAPIQPS isn't throttling)
- Nodes reporting NotReady (typically certificate expiration or kubelet crashes)
Run kubectl describe node <node-name> to see critical kubelet conditions like Ready, MemoryPressure, DiskPressure, and PIDPressure. A NotReady condition almost always indicates kubelet failure.
Pod Health Probes
The kubelet implements three probe types:
- Liveness probes: Restart failed containers
- Readiness probes: Determine if a pod should receive traffic
- Startup probes: Handle slow-starting applications
Each probe type supports HTTP, TCP, and exec methods. Misconfigured probes appear frequently on CKA exam scenarios.
Pod Lifecycle Management and Eviction
The kubelet manages the complete pod lifecycle from initial scheduling through final termination. Understanding each stage is crucial for CKA success.
Pod Lifecycle Stages
When a pod is scheduled to a node, the kubelet executes this sequence:
- Pulls the container image (if not already cached)
- Creates the container using the container runtime
- Sets up networking through CNI plugins
- Mounts volumes
- Starts monitoring for health and resource violations
Pod lifecycle states are:
- Pending: Being scheduled and pulled
- Running: Containers executing
- Succeeded: Completed successfully
- Failed: Containers crashed
- Unknown: Lost contact with kubelet
Eviction and QoS Classes
Pod eviction occurs when node resources become scarce. The kubelet monitors memory and disk pressure, triggering eviction based on QoS class:
- Guaranteed: Resource requests equal limits (evicted last)
- Burstable: Partial resource limits (evicted second)
- BestEffort: No resource limits (evicted first)
For CKA, configure eviction thresholds using flags like --eviction-hard and --eviction-soft.
Graceful Termination
When a pod is deleted, the kubelet sends SIGTERM to containers and waits for terminationGracePeriodSeconds (default 30 seconds) before forcefully killing them with SIGKILL. This allows applications to gracefully shut down connections.
PreStop Hooks and Node Maintenance
PreStop hooks allow custom cleanup logic before termination. The kubelet also handles node maintenance:
- Cordon: Prevents new pods from scheduling
- Drain: Forcefully evicts existing pods
Understand when to use kubectl cordon versus kubectl drain for cluster maintenance.
Kubelet Certificates, Security, and CKA Exam Strategy
The kubelet uses TLS certificates to authenticate with the API server and secure its own API endpoint. Certificate management and security are heavily tested on CKA.
Certificate Locations and Rotation
The kubelet certificate is located at /var/lib/kubelet/pki/kubelet.crt with the private key at /var/lib/kubelet/pki/kubelet.key. Certificate expiration is a common failure scenario.
Kubernetes 1.26+ enables automatic kubelet certificate rotation, but understand manual rotation. Check certificate expiration:
openssl x509 -in /var/lib/kubelet/pki/kubelet.crt -text -noout
Enable automatic rotation with these flags:
--rotate-certificates: Enable client certificate rotation--rotate-server-certificates: Enable server certificate rotation
Kubelet API Security
The kubelet API on port 10250 requires proper authentication through client certificates. Verify connectivity using curl:
curl -k --cert kubelet.crt --key kubelet.key https://node-ip:10250/api/v1/pods
The kubelet implements authorization through the API server, checking if requests are authorized using the system:nodes ClusterRole.
CKA Exam Focus Areas
Prioritize these practical scenarios:
- Diagnose why nodes report NotReady status due to certificate issues
- Manually rotate expired certificates
- Verify kubelet can communicate with the API server
- Check ServiceAccount integration with kubelet authentication
Flashcard Study Strategy
Create cards focused on:
- Certificate locations and expiration diagnosis
- Eviction policy configuration and QoS classes
- Pod lifecycle state transitions and probe types
- Scenario-based troubleshooting for NotReady nodes
- Common kubelet flags and configuration parameters
Build your deck with real CKA exam scenarios where you must diagnose why a node fails or pods don't schedule. This mirrors actual exam questions and reinforces practical Kubernetes administration.