Kubernetes Services: Types and Use Cases
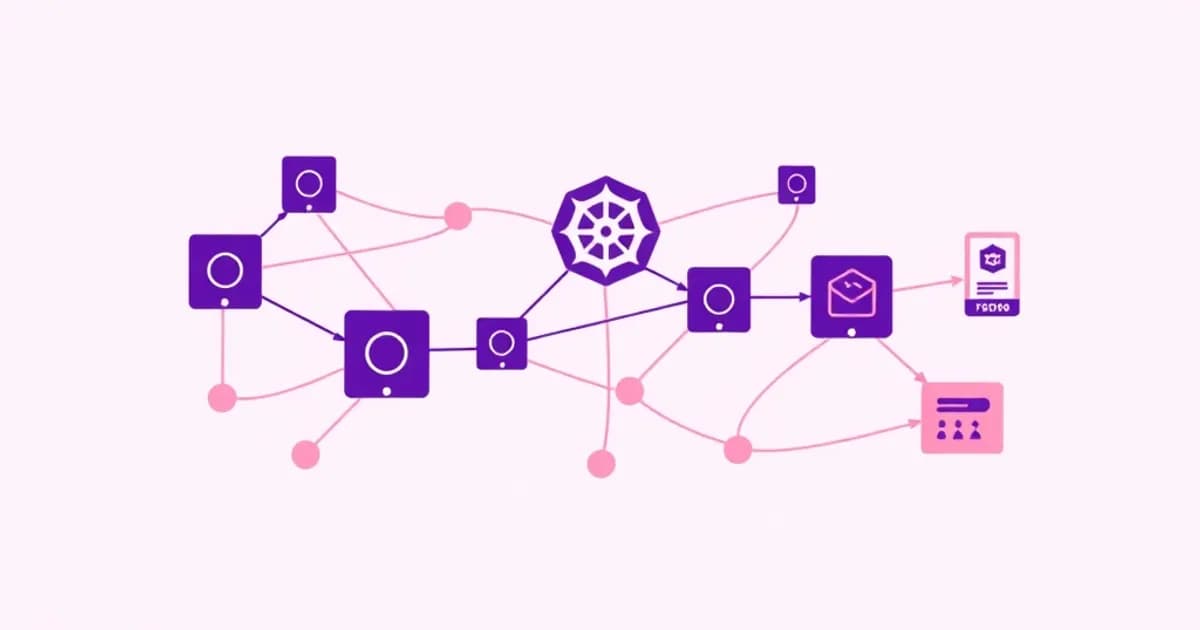
A Kubernetes Service is an abstraction that defines a logical set of pods and a policy for accessing them. Services enable loose coupling between microservices by providing a stable endpoint for communication.
The Four Service Types
There are four primary service types, each serving different networking needs.
- ClusterIP: The default type. Creates a virtual IP accessible only from within the cluster. Ideal for internal communication between pods.
- NodePort: Extends ClusterIP by opening a specific port on every node (range 30000-32767). Allows external traffic to reach services on a static port.
- LoadBalancer: Builds on NodePort and provisions an external load balancer from the cloud provider. Enables true external access without manual port management.
- ExternalName: Allows services to reference external DNS names. Useful for integrating with services outside the cluster.
Each service type builds upon the previous one, providing increasing levels of external accessibility.
Understanding Service Networking
When studying services, focus on understanding the networking flow. Learn how traffic reaches a service through iptables rules or IPVS. Understand how endpoints are automatically managed when pods scale up or down. Study how service discovery works through DNS.
Practice creating services with different types. Learn their YAML specifications, particularly the spec.type, spec.ports, and spec.selector fields. Real-world scenarios often involve choosing the appropriate service type based on requirements, debugging connectivity issues, and understanding how services maintain state across pod deletions and recreations.
Advanced Networking: Ingress and Network Policies
Ingress provides a layer-7 (application-level) routing solution for managing external access to services within a cluster. Unlike Services which operate at layer 4, Ingress enables hostname-based routing, path-based routing, and SSL/TLS termination.
Ingress Resources and Controllers
An Ingress resource defines rules for routing traffic. However, it requires an Ingress controller to actually implement those rules. Common controllers include NGINX, HAProxy, and cloud-specific implementations.
Understanding the relationship between Ingress resources and controllers is crucial. The resource is merely configuration, while the controller watches for changes and configures the underlying load balancer or proxy. For the CKA exam, practice writing Ingress rules that route different hostnames or paths to different services, configure TLS certificates, and troubleshoot routing issues.
Network Policies and Zero-Trust Security
Network Policies are Kubernetes objects that specify how pods can communicate with each other and with external endpoints. By default, all pods in a cluster can communicate with each other. Network Policies enforce deny-by-default rules, allowing only explicitly permitted traffic.
Policies work through label selectors to target specific pods. They define ingress (inbound) and egress (outbound) rules. A well-designed network policy strategy implements the principle of least privilege, where each pod receives only the minimum necessary network access.
On the CKA exam, expect questions about designing network policies to segment traffic. Understand traffic flow with multiple policies. Practice debugging why policies are blocking legitimate communication. Write policies that allow microservices to communicate while blocking unauthorized access from untrusted pods.
DNS Resolution and Service Discovery in Kubernetes
Kubernetes provides automatic DNS resolution for services, enabling pods to discover and communicate with each other using human-readable names rather than IP addresses. The DNS system assigns names using the pattern service-name.namespace.svc.cluster.local. Shorter forms like service-name.namespace and service-name work depending on the pod's namespace.
CoreDNS and Service Discovery
CoreDNS is the default DNS server in modern Kubernetes clusters. It runs as a deployment in the kube-system namespace. It watches the Kubernetes API for service and pod creation events and automatically updates DNS records accordingly.
Understanding DNS resolution is critical for debugging connectivity issues. If a pod cannot reach a service by name, the problem might involve DNS configuration, CoreDNS pod availability, or the DNS search path configuration in the pod's /etc/resolv.conf. For the CKA exam, be comfortable debugging DNS issues using tools like nslookup, dig, and kubectl exec to run DNS queries from within pods.
The Endpoint Controller
Service discovery works bidirectionally. Pods discover services through DNS. The service discovers healthy pods through the Kubernetes API's endpoint controller. The endpoint controller continuously monitors pods matching a service's label selector. It maintains the Endpoints object, which stores the list of IP addresses and ports of active pods.
When a pod terminates or becomes unhealthy, the endpoint controller removes it from the endpoints list. This automatically removes it from the service's rotation. Practice scenarios that involve understanding how DNS resolution works across namespaces, configuring custom DNS policies, and verifying that services and pods are properly registered in DNS.
Troubleshooting Network Connectivity Issues
Network troubleshooting is a significant portion of the CKA exam, often appearing in performance-based scenarios. The systematic approach to troubleshooting involves checking connectivity layer by layer. First verify pod-to-pod communication, then pod-to-service communication, then check external access.
Step-by-Step Troubleshooting Process
Start by confirming that pods exist and are running using kubectl get pods. Then verify that services exist and have endpoints with kubectl get svc and kubectl get endpoints. Use kubectl exec to enter a pod and test connectivity to other pods or services using ping, curl, or netcat.
Check if DNS is resolving correctly using nslookup or dig commands from within a pod. Examine service definitions carefully. A common issue is label selector mismatches where the service definition doesn't match any pods, resulting in no endpoints.
Checking Network Policies and External Access
For NodePort and LoadBalancer services, verify that traffic reaches the nodes. Check that the node ports are actually listening. Review network policies to ensure they're not blocking legitimate traffic. Remember that policies use AND logic for multiple selectors and are namespace-scoped.
Examine firewall rules and security groups if accessing services from outside the cluster. Review kube-proxy configuration and logs, as this component implements the actual networking rules. Use iptables rules or IPVS configurations to trace how traffic is being routed. Develop a mental model of Kubernetes networking that includes understanding virtual networking, service abstractions, and how the control plane components maintain network state.
Study Strategies and CKA Exam Preparation for Networking
Kubernetes networking topics require both conceptual understanding and hands-on practice, making them ideal for flashcard-based learning combined with practical labs. Create flashcards for key concepts like service types, their use cases, and the networking implications of each.
Building Your Flashcard Deck
Include command-based flashcards that test your ability to recall kubectl syntax for creating services, defining network policies, and debugging connectivity issues. Practice writing YAML manifests for different service types without reference materials. The exam environment provides limited documentation access.
Set up a local Kubernetes cluster using minikube, kind, or kubeadm. Create multi-container applications with multiple services to understand real-world networking scenarios. Deploy network policies and intentionally test edge cases, like policies that block all traffic or policies with conflicting rules.
Exam Timeline and Speed Practice
The CKA exam allocates approximately 2 to 3 hours for testing. Networking topics likely appear in multiple scenarios. Plan to spend 2 to 3 weeks studying services and networking if you're new to Kubernetes. Focus first on understanding how each service type works, then practice troubleshooting scenarios.
Create flashcards that test your ability to recognize networking issues from symptom descriptions. Recommend solutions based on common problems. Remember that CKA is performance-based, so practice speed alongside accuracy. You should be able to create a service definition and verify connectivity in under five minutes.