Understanding Kubernetes Architecture and Core Components
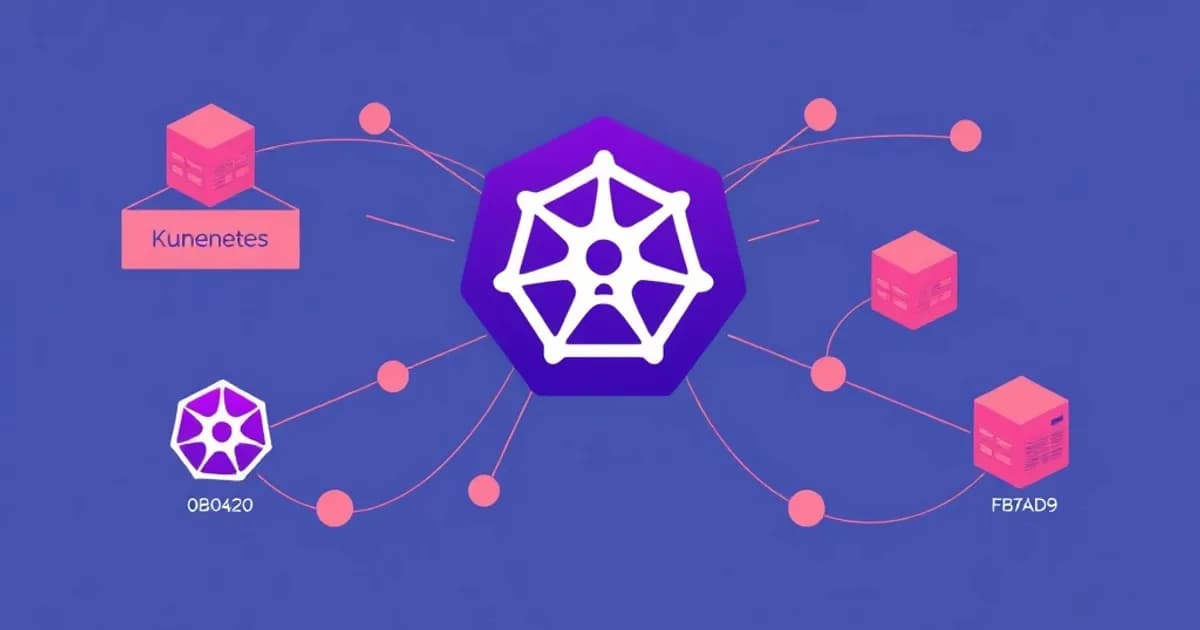
Kubernetes uses a master-worker architecture where the control plane manages cluster state. Worker nodes run your applications.
Control Plane Components
The control plane contains several critical parts:
- API server: Gateway for all cluster operations
- etcd: Distributed key-value store holding all cluster data
- Scheduler: Assigns pods to nodes based on resource requirements
- Controller manager: Runs controllers that maintain desired cluster state
Worker Node Components
Each worker node runs the kubelet agent, which communicates with the API server and manages pod lifecycle. The kube-proxy handles networking and load balancing for services.
Understanding how these components interact is fundamental to troubleshooting cluster issues. When the scheduler fails, new pods remain in Pending state. This relationship-based thinking is essential for the CKA exam.
Focus on how changes to one component affect the entire system. Study how the scheduler, API server, and controller manager work together to maintain cluster state. This systems-thinking approach prepares you for the exam's performance-based questions and real-world administration tasks.
Workload Management: Pods, Deployments, and StatefulSets
Pods are the smallest deployable units in Kubernetes, typically containing one container. Multi-container pods exist for sidecar patterns. Understanding pod lifecycle states is crucial.
Pod Lifecycle States
- Pending: Pod hasn't been scheduled yet
- Running: Active execution in progress
- Succeeded: Container exited with code 0
- Failed: Container exited with non-zero code
- Unknown: Communication with node was lost
Deployment and StatefulSet Differences
Deployments manage stateless applications with interchangeable replicas. They support rolling updates, rollbacks, and scaling. Use them for web servers, APIs, and microservices.
StatefulSets manage stateful applications requiring stable network identities. Each replica receives an ordinal number (0, 1, 2) and predictable hostname. Use them for databases and message queues.
Other Workload Types
DaemonSets ensure a pod runs on every node, useful for logging agents. Jobs create pods that run to completion. CronJobs schedule jobs at specific times.
The CKA exam tests your ability to create, update, and troubleshoot these workloads. Practice writing YAML manifests and understanding resource requests, lifecycle hooks like readinessProbes and livenessProbes.
Networking and Service Discovery in Kubernetes
Kubernetes networking allows pod-to-pod communication across the cluster through container network interfaces (CNI). Every pod receives its own IP address and communicates directly without NAT.
Services and Service Types
Services provide stable endpoints for accessing pods, abstracting away individual pod IP changes. Choose the right type for your needs:
- ClusterIP: Internal cluster DNS names and load balancing
- NodePort: Expose on specific port on every node for external access
- LoadBalancer: Integrate with cloud providers for external load balancers
Service Discovery and Ingress
Services receive automatic DNS names like my-service.default.svc.cluster.local. This enables automatic service discovery within clusters.
Ingress controllers manage external HTTP/HTTPS routing based on hostnames and paths. They are essential for production deployments.
Network Security
NetworkPolicies act as firewalls for pod-to-pod communication. They allow you to restrict traffic between pods and namespaces. Understanding these policies is critical for the CKA exam.
Practice working with different service types, creating Ingress resources, and understanding DNS resolution. Pay special attention to how label selectors drive all resource selection in Kubernetes.
Storage and Configuration Management
Kubernetes abstracts storage through multiple layers. Understanding the relationship between these components is essential for the CKA exam.
Storage Components
- Volumes: Provide ephemeral or persistent storage for pods
- PersistentVolumes (PVs): Represent actual storage resources in the cluster
- PersistentVolumeClaims (PVCs): Allow pods to request storage without knowing implementation details
Storage classes enable dynamic provisioning. They automatically create PVs when PVCs are requested, eliminating manual PV creation.
Volume Types and Use Cases
- emptyDir: Temporary pod storage
- hostPath: Node-local storage (generally avoided in production)
- configMap: Configuration data
- secret: Sensitive information
- Cloud-specific types: awsElasticBlockStore, azureDisk
Configuration and Secrets
ConfigMaps store non-sensitive configuration like properties files or JSON. Secrets encode sensitive data in base64 (note: not truly encrypted by default). You can mount these as files or inject them as environment variables.
Practice creating storage classes, understanding access modes (ReadWriteOnce, ReadOnlyMany, ReadWriteMany), and debugging PVC issues where claims remain unbound.
Security, RBAC, and Cluster Administration
Security in Kubernetes operates at multiple levels. Authentication identifies users. Authorization determines what authenticated users can do. Admission controllers enforce policy.
Role-Based Access Control (RBAC)
RBAC is the primary authorization mechanism. Roles and ClusterRoles define rules for resources and verbs (get, list, create, delete). RoleBindings and ClusterRoleBindings associate roles with users, groups, or service accounts.
Understanding fine-grained permissions is crucial for the CKA exam and production administration.
Service Accounts and Pod-Level Identity
ServiceAccounts provide pod-level identity. You restrict what each pod can do through RBAC. Network Policies complement RBAC by restricting network traffic between pods and namespaces.
Pod Security and Namespaces
Pod Security Policies or Pod Security Standards enforce security configurations. They prevent privileged containers or require read-only root filesystems. Namespaces provide logical cluster partitioning, allowing multiple teams to share a cluster while maintaining resource quotas.
Practice creating RBAC rules from scratch. Understand the principle of least privilege. Use kubectl to audit permissions. Additionally, understand how service accounts and tokens work for pod authentication to the API server.